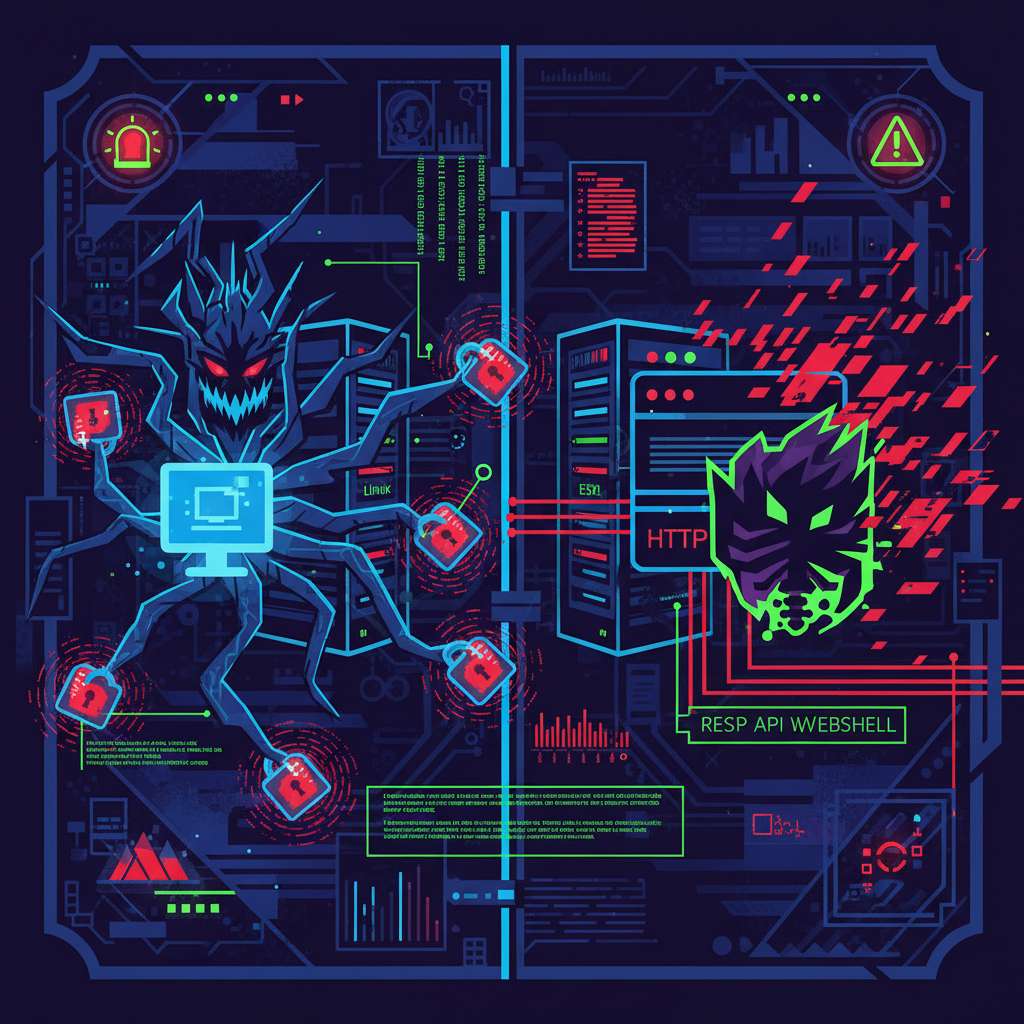
Kraken ransomware adds CPU/IO benchmarking—what to hunt before the encryptor runs
On November 13, 2025, reporting highlighted that the cross-platform Kraken ransomware profiles victim machines first, benchmarking disk/CPU to choose between full or partial encryption and tune threads to avoid tripping resource alarms BleepingComputer. Cisco Talos’ deep dive confirms host-side performance tests via a temporary file and command-line switches, plus distinct encryptors for Windows and Linux/VMware ESXi that append “.zpsc” and drop “readme_you_ws_hacked.txt” Talos. Talos also notes ties to the older HelloKitty operation and a Kraken-hosted forum announcement (“The Last Haven Board”), a link also observed by independent analysis of Kraken’s leak site Talos Cyjax.